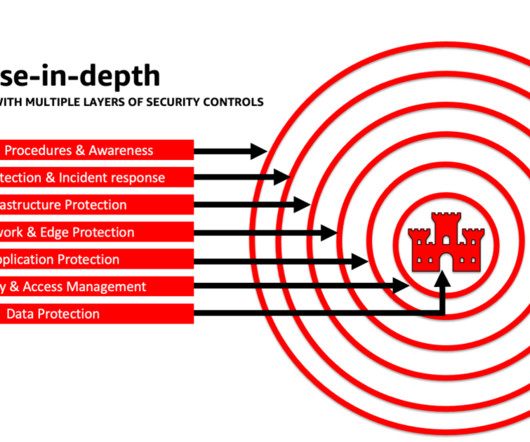
Architect defense-in-depth security for generative AI applications using the OWASP Top 10 for LLMs
AWS Machine Learning
JANUARY 26, 2024
Some risks may be acceptable to your business, and a threat modeling exercise can help your company identify what your acceptable risk appetite is. Define strict data ingress and egress rules to help protect against manipulation and exfiltration using VPCs with AWS Network Firewall policies.










Let's personalize your content